


Use these practices to avoid handing your RRC Polytech (RRC) account and password or personal information to a criminal.
Scam artists often go phishing for private information. They will send you an email which appears to be from a legitimate source like a bank, government agency, or even RRC, or give you a form or a link that looks authentic, and then ask you to provide personal account and personal information. Before you know it—you’re a victim!
Here is what you can do to avoid taking the bait and falling prey to phishing scams:
Phishing emails typically include upsetting or exciting language to get you to react without thinking, such as, “Your password is about to expire—respond now.” They will ask you for your user name and password, credit card number, Social Insurance Number, date of birth, or other personal information.
If you suspect that the message you received is not authentic or if you do not know the sender, do not use the links in the email. Instead, call the company or type the website address directly into your browser.
Make it a habit to log on regularly and check your accounts to verify that all transactions are legitimate.
Instead, use a secure website, phone call, or an office visit to communicate with financial institutions and other organizations.
Phishers can forge two indicators of a secure site: the https:// and the yellow lock. Instead of using the provided link, always type the web address of your financial institution directly into your browser. To test the security lock, double‑click the lock to display the security certificate for the site. If any type of warning displays, such as, “the address of the site does not match the certificate,” do NOT continue.
For example, if a link directs you to PayPal, notice what the address bar displays. If you see something like http://www.scammedyou.com/paypal/login.html, do NOT continue.
While you cannot stop phishing attempts, you can refuse to take the bait. Exercise caution, verify your sources, and provide information only when you know you are communicating with the actual organization, organizations like RRC Polytech—that put privacy and security first.
If you fall victim to a phishing attack, you should take the following steps to ensure that your account is secure:
If your account is still accessible, change your password as soon as possible. The longer someone has your credentials, the more harm they can cause. Please open the Change your password page.
Submit an emergency IT support ticket at the ITS Service Desk.
If you still have the phishing message, mark it as junk. Right-click on the message, and then select Mark as junk.
In an attempt to phish additional victims, attackers may add links to your email signature.
Some attackers may set your account to automatically forward all email to an account they control. Check to make sure that attackers are not forwarding your emails to another address.
Attackers may add filters to hide their activities from the account owner. Check to make sure that no one has created new Inbox rules.
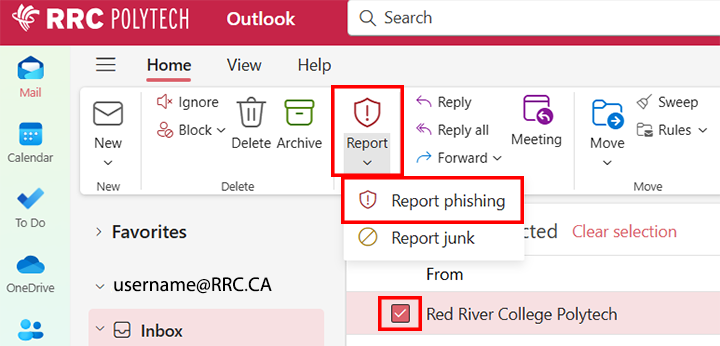
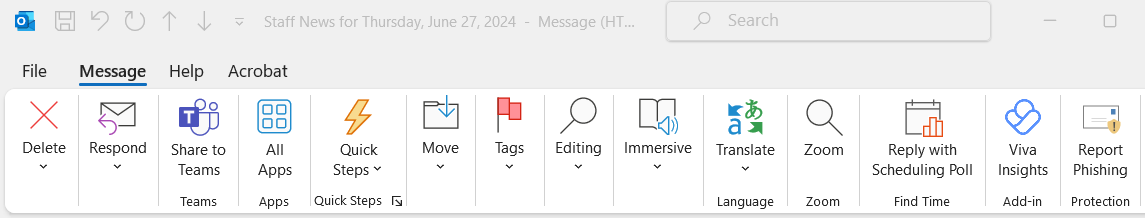
If you receive an email that you suspect is phishing or malicious, you can report it to ITS for evaluation by using one of the following two options.
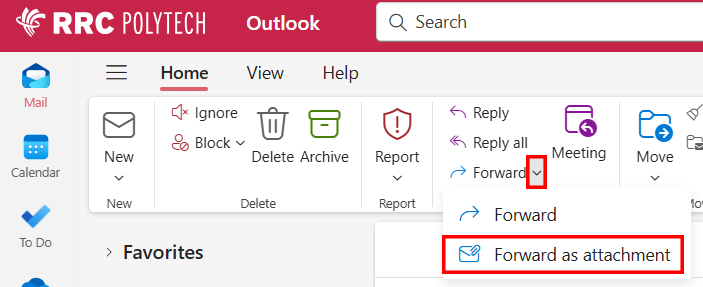
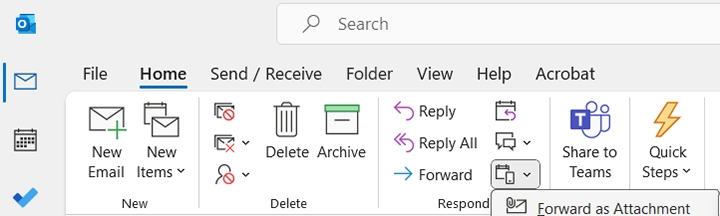
Add this email address phishbowl@rrc.ca in the To field of your email message, and then send the email.
Log on to HUB, open Applications, and then click the Cyber Security Training (KnowBe4) icon for current IT Security training to help you keep your home and work computers safe.
![]()
RRC Polytech campuses are located on the lands of the Anishinaabeg, Ininiwak, Anishininwak, Dakota Oyate, and Denésuline, and the National Homeland of the Red River Métis.
We recognize and honour Treaty 3 Territory Shoal Lake 40 First Nation, the source of Winnipeg’s clean drinking water. In addition, we acknowledge Treaty Territories which provide us with access to electricity we use in both our personal and professional lives.